Network Hacking Continued As mentioned earlier, courses that promote or teach hacking or illegal activities are against the terms of service of most reputable online learning platforms, including Udemy.
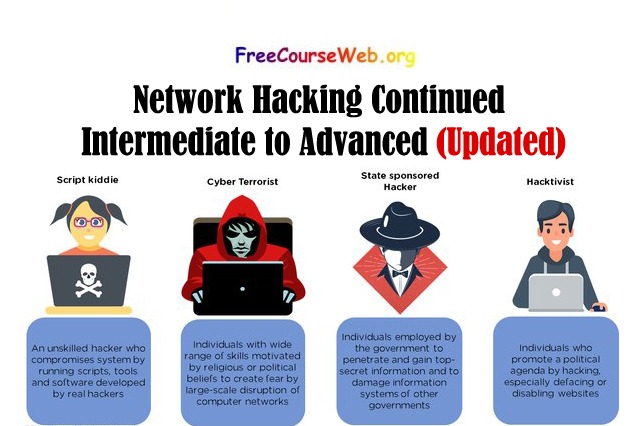
However, courses that cover legitimate and ethical network security topics may include some of the following:
- Network Penetration Testing: Techniques and tools for testing network security, identifying vulnerabilities, and exploiting weaknesses.
- Advanced Exploitation Techniques: Advanced methods for exploiting vulnerabilities, including buffer overflows, race conditions, and other complex attacks.
- Network Reconnaissance and Enumeration: Techniques for discovering and mapping network resources, including ports, services, and operating systems.
- Cryptography and Encryption: Principles and applications of cryptography, including encryption, decryption, digital signatures, and certificates.
- Network Defense and Mitigation: Strategies and tools for protecting networks from attacks, including intrusion detection and prevention, firewalls, and other security measures.
- Web Application Security: Techniques for securing web applications against common attacks, including cross-site scripting (XSS), SQL injection, and other vulnerabilities.
- Incident Response and Forensics: Procedures and tools for detecting, analyzing, and responding to security incidents, including malware analysis, data recovery, and legal issues.
Complete Ethical Hacking Free Bootcamp
Web Security & Bug Bounty Free Penetration Testing
Ethical Hacking: Black Hat Techniques Free
What you’ll learn
An intermediate to advanced network hacking course might cover:
- Network reconnaissance techniques
- Scanning and enumeration of network services and hosts
- Exploitation of vulnerabilities in network services and hosts
- Privilege escalation techniques to gain higher-level access
- Post-exploitation techniques, such as maintaining access and covering tracks
- Advanced techniques for evading detection and avoiding countermeasures, such as firewalls, intrusion detection systems, and antivirus software
- Social engineering and phishing attacks to gain access to sensitive information
- Wireless network hacking, including attacking WEP and WPA2-PSK encryption
- Web application hacking, including SQL injection and cross-site scripting (XSS) attacks
- Reverse engineering of software and firmware to discover vulnerabilities
It is important to note that hacking without authorization is illegal and unethical. Therefore, it’s essential to use the knowledge of network security for ethical purposes only.
How to Earn Money with EarnKaro: A Step-by-Step Guide
Requirements
- Basic understanding of networking protocols and concepts, such as TCP/IP, DNS, and routing
- Familiarity with operating systems such as Linux and Windows
- Understanding of programming concepts and scripting languages such as Python or Bash
- Familiarity with tools commonly used in network hacking, such as Metasploit, Nmap, Wireshark, and Burp Suite
- A dedicated computer or virtual machine for lab exercises, with sufficient resources to run multiple virtual machines and network simulations
- A willingness to continuously learn and keep up-to-date with the latest techniques and tools in the field of network hacking.
Course Content
I can provide a general outline of what an intermediate to advanced network hacking course might cover:
Module 1: Introduction to Network Hacking
- Overview of network hacking
- Legal and ethical considerations
- Setting up a lab environment
- Review of basic networking concepts
Module 2: Network Reconnaissance Techniques
- Passive and active reconnaissance
- Information gathering using tools like Google Dorks, Whois, and Shodan
- Identifying targets, such as hosts, IP ranges, and open ports
Module 3: Scanning and Enumeration
- Port scanning techniques using Nmap
- Enumeration of network services and hosts using tools like Nessus and OpenVAS
- Vulnerability scanning and assessment
Module 4: Exploitation
- Finding and exploiting vulnerabilities in network services and hosts
- Tools and techniques for exploiting buffer overflows, SQL injection, and other common vulnerabilities
- Exploiting misconfigured services, such as FTP and Telnet
Module 5: Privilege Escalation
- Techniques for escalating privileges to gain higher-level access to systems
- Identifying and exploiting weaknesses in user authentication and authorization
Module 6: Post-Exploitation
- Maintaining access to a compromised system
- Covering tracks and avoiding detection
- Gathering sensitive information without raising suspicion
Module 7: Advanced Evasion Techniques
- Techniques for bypassing security measures, such as firewalls and intrusion detection systems
- Methods for evading antivirus software
Module 8: Social Engineering and Phishing Attacks
- Techniques for tricking people into revealing sensitive information
- Phishing attacks using email, phone, and social media
Module 9: Wireless Network Hacking
- Cracking WEP and WPA2-PSK encryption
- Attacking wireless networks using tools like Aircrack-ng and Reaver
Module 10: Web Application Hacking
- Identifying and exploiting vulnerabilities in web applications, such as SQL injection and cross-site scripting (XSS) attacks
- Introduction to web application penetration testing using tools like Burp Suite
Module 11: Reverse Engineering
- Reverse engineering of software and firmware to discover vulnerabilities
- Debugging and disassembly using tools like OllyDbg and IDA Pro
Module 12: Conclusion
- Final thoughts on network hacking
- Continuing education and keeping up-to-date with the latest techniques and tools
- Ethical and legal considerations for using network hacking skills.