Elevating Security Awareness In the rapidly evolving digital landscape, security awareness training has become an imperative for individuals
Organizations alike. Elevating Security Awareness This comprehensive guide aims to delve into the essence of security awareness training, its importance, key components, and strategies to empower individuals and teams in safeguarding against cyber threats.
Elevating Security Awareness
I. Understanding Security Awareness Training
1. Definition:
Security awareness training is an educational process designed to equip individuals with the knowledge and skills to recognize, prevent, and respond to cybersecurity threats. It fosters a culture of security consciousness within an organization.
2. Target Audience:
Security awareness training is relevant for employees at all levels of an organization, from executives to front-line staff. It also extends to individuals in their personal digital lives.
II. Key Components of Security Awareness Training
1. Phishing Awareness:
Training on recognizing and avoiding phishing attempts, which are common tactics used by cybercriminals to trick individuals into divulging sensitive information.
2. Password Best Practices:
Education on creating strong passwords, implementing multi-factor authentication, and the importance of regularly updating and safeguarding login credentials.
3. Device Security:
Guidance on securing personal and corporate devices, including the installation of security updates, using antivirus software, and implementing device encryption.
4. Data Protection:
Training on handling sensitive data responsibly, understanding data classification, and adhering to privacy regulations and policies.
5. Social Engineering Awareness:
Awareness of social engineering tactics, such as pretexting and baiting, and strategies to avoid falling victim to manipulative schemes.
6. Incident Response Training:
Education on recognizing and reporting security incidents promptly, ensuring a swift and coordinated response to mitigate potential damage.
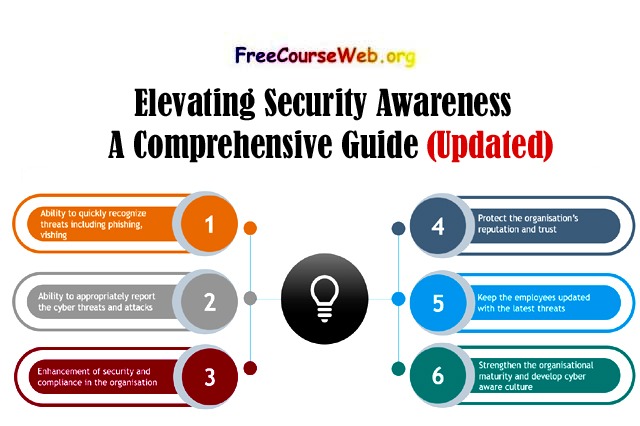
III. Importance of Security Awareness Training
1. Risk Mitigation:
Security awareness training mitigates the risk of security breaches by empowering individuals to recognize and respond to potential threats proactively.
2. Compliance and Regulations:
Many industries and regions have specific cybersecurity regulations. Security awareness training ensures compliance with these regulations, avoiding legal consequences.
3. Cultural Shift:
Fosters a culture of cybersecurity within organizations, where security becomes a shared responsibility rather than solely the concern of IT professionals.
IV. Strategies for Effective Security Awareness Training
1. Regular Training Modules: Elevating Security Awareness
Implement regular, bite-sized training modules to keep security awareness fresh in the minds of individuals. Consistency is key for long-term effectiveness.
2. Simulated Phishing Exercises: Elevating Security Awareness
Conduct simulated phishing exercises to test the ability of individuals to identify phishing attempts and provide immediate feedback on their actions.
3. Interactive Workshops and Webinars: Elevating Security Awareness
Engage employees through interactive workshops and webinars that address specific cybersecurity topics and allow for questions and discussions.
4. Gamification:
Introduce gamification elements, such as quizzes and challenges, to make the learning experience more enjoyable and encourage active participation.
5. Customization for Roles:
Tailor training content to the specific roles and responsibilities of individuals within the organization, ensuring relevance and practical application.
V. Measuring the Effectiveness of Security Awareness Training
1. Phishing Simulation Metrics:
Track metrics from simulated phishing exercises, such as click-through rates and user responsiveness, to gauge improvements over time.
2. Incident Response Evaluation:
Assess the effectiveness of incident response by monitoring the time it takes for individuals to report security incidents and the accuracy of their responses.
3. Knowledge Assessments:
Conduct periodic knowledge assessments to measure the retention and understanding of security awareness concepts.
VI. Challenges and Considerations
1. Overcoming Employee Resistance:
Address potential resistance to security awareness training by emphasizing its relevance, providing real-world examples, and highlighting the collective responsibility for cybersecurity.
2. Adapting to Evolving Threats:
Continuously update training content to address emerging cybersecurity threats and tactics, ensuring that individuals remain equipped to face the evolving landscape.
VII. Building a Security-Aware Culture Beyond the Workplace
1. Personal Cybersecurity Awareness:
Extend security awareness training to individuals’ personal lives, emphasizing the importance of practicing good cybersecurity habits outside of the workplace.
2. Family and Community Engagement:
Encourage employees to share security awareness knowledge with their families and communities, contributing to a broader culture of cybersecurity.
Mastering Collaboration: Work Together Best Results
Business Writing Skills Course 87% Free
Cryptocurrency Wallets: A Comprehensive Guide
Liquidity Risk: Impact, Role & Challenges
What is Income? Defination, Types & Concept
VIII. Conclusion: Empowering a Resilient Digital Society
In conclusion, security awareness training stands as a linchpin in the defense against cyber threats, fostering a proactive and resilient digital society. By understanding its key components, embracing effective strategies, and continually adapting to the evolving threat landscape, individuals and organizations can create a culture where cybersecurity is ingrained in every digital interaction.