“Learn Ethical Hacking From Scratch” is an online course available on Udemy, which aims to teach participants the basics of ethical hacking.

The course is designed for beginners who have little or no knowledge about hacking, but are interested in learning about it.
The course is divided into different sections, and each section covers a specific topic related to ethical hacking. The sections are as follows:
Ethical Hacking Beginner to Advanced Free Course
Ethical Hacking Beginner To Expert Free Course
Complete Ethical Hacking Course
Network Hacking Continued Intermediate to Advanced
- Introduction: In this section, the instructor introduces the course and explains the basics of ethical hacking.
- Information Gathering: This section covers the methods and techniques used to gather information about a target system or network.
- Scanning: This section explains how to scan a network or system to identify vulnerabilities and weaknesses.
- Enumeration: This section covers the process of gathering information about users, systems, and applications in a network.
- Vulnerability Assessment: This section explains how to identify and evaluate vulnerabilities in a network or system.
- Exploitation: This section covers the techniques used to exploit vulnerabilities and gain access to a system or network.
- Post-Exploitation: This section explains what to do after gaining access to a system, such as maintaining access and covering tracks.
- Web Application Hacking: This section covers the techniques used to hack web applications, including SQL injection, cross-site scripting (XSS), and file inclusion.
- Wireless Network Hacking: This section explains how to hack wireless networks, including Wi-Fi networks.
- Social Engineering: This section covers the techniques used to manipulate people into giving up sensitive information.
- Conclusion: In this section, the instructor summarizes the course and provides some final thoughts.
The course includes practical exercises and demonstrations to help participants understand the concepts and techniques covered in each section. The instructor also provides downloadable resources, including cheat sheets and tools, to help participants practice what they have learned.
It’s important to note that the course is focused on ethical hacking, which means that the techniques and methods taught are legal and ethical. The course emphasizes the importance of obtaining permission before testing or hacking any system or network. Ethical Hacking From Scratch
Overall, “Learn Ethical Hacking From Scratch” is a comprehensive course that covers the basics of ethical hacking in a structured and easy-to-understand manner. It is a good starting point for beginners who want to learn about ethical hacking and cybersecurity.
How to Earn Money with EarnKaro: A Step-by-Step Guide
How to Earn Money from Website
How to Earn Money from Social Media? Top 10 Ways
Ethical Hacking From Scratch course content
The “Ethical Hacking From Scratch” course on Udemy covers a wide range of topics related to ethical hacking. Here is a detailed breakdown of the course content: Ethical Hacking From Scratch
1. Introduction
- Course Overview
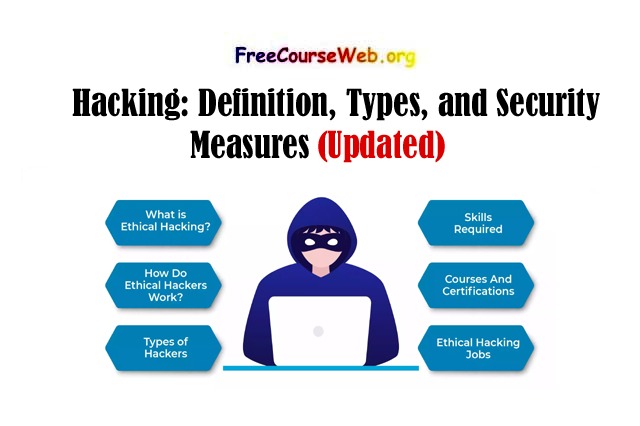
- What is Ethical Hacking?
- Types of Hackers
- Terminologies used in Ethical Hacking
2. Setting Up Your Environment
- Setting up a Virtual Machine
- Installing Kali Linux
- Installing VirtualBox and VMware
3. Linux Basics
- Basic Linux Commands
- File System Structure
- Understanding Permissions
- Installing and Removing Software
4. Information Gathering
- Introduction to Information Gathering
- Google Hacking
- DNS Enumeration
- Port Scanning
- Whois Lookup
- Social Engineering
5. Scanning
- Introduction to Scanning
- Ping Sweeps
- Nmap Basics
- Nmap Scripting Engine
- Vulnerability Scanning
6. Enumeration
- Introduction to Enumeration
- SNMP Enumeration
- SMB Enumeration
- LDAP Enumeration
- NetBIOS Enumeration
- SMTP Enumeration
7. System Hacking
- Introduction to System Hacking
- Password Cracking
- Escalating Privileges
- Backdoors and Rootkits
- Trojans and Malware
- Metasploit Basics
8. Network Hacking
- Introduction to Network Hacking
- Packet Sniffing
- ARP Poisoning
- DNS Spoofing
- MITM Attacks
- DoS and DDoS Attacks
9. Web Application Hacking
- Introduction to Web Application Hacking
- SQL Injection
- Cross-Site Scripting (XSS)
- Cross-Site Request Forgery (CSRF)
- File Inclusion
- Remote File Inclusion (RFI)
10. Wireless Hacking
- Introduction to Wireless Hacking
- Wireless Security Standards
- Wi-Fi Encryption
- Cracking WEP and WPA2
- Evil Twin Attacks
11. Social Engineering
- Introduction to Social Engineering
- Pretexting
- Baiting
- Phishing
- Spear Phishing
- Watering Hole Attacks
12. Conclusion
- Course Summary
- Next Steps
Ethical Hacking From Scratch course requriment
To take the “Ethical Hacking From Scratch” course on Udemy, you will need the following requirements:
A computer: You will need a computer with at least 4GB of RAM and a modern processor. The course is taught using Kali Linux, so your computer must be capable of running a virtual machine.
Internet access: You will need a reliable internet connection to download the required software and virtual machines. The course includes many practical exercises that require internet access.
Basic knowledge of computer networks: You should have a basic understanding of computer networks and how they work. This includes knowledge of IP addresses, TCP/IP, and network protocols.
Basic Linux knowledge: The course is taught using Kali Linux, so you should have some basic knowledge of the Linux operating system, including file system structure and basic commands.
A willingness to learn: The course is designed for beginners with no prior knowledge of ethical hacking. However, you must be willing to put in the effort to learn and practice the concepts covered in the course.
A Udemy account: You will need to create a Udemy account to enroll in the course. Udemy offers both free and paid options, so you can choose the option that suits you best.